Expose Istio¶
In this section you will expose Istio and the services running behind it using the NGINX Ingress Controller. TLS termination will happen at the ALB in front of NGINX.
Fast Forward
If you have already exposed Istio for serving, expand this box to fast-forward.
- Proceed to the Verify section.
Choose one of the following options to expose Istio:
Overview
What You’ll Need¶
- A configured management environment.
- Your clone of the Arrikto GitOps repository.
- An existing EKS cluster.
- A working AWS Load Balancer Controller deployment.
- A working NGINX Ingress Controller deployment.
Option 1: Expose Istio Automatically (preferred)¶
Under construction
This section is a work in progress. Use Option 2: Expose Istio Manually instead.
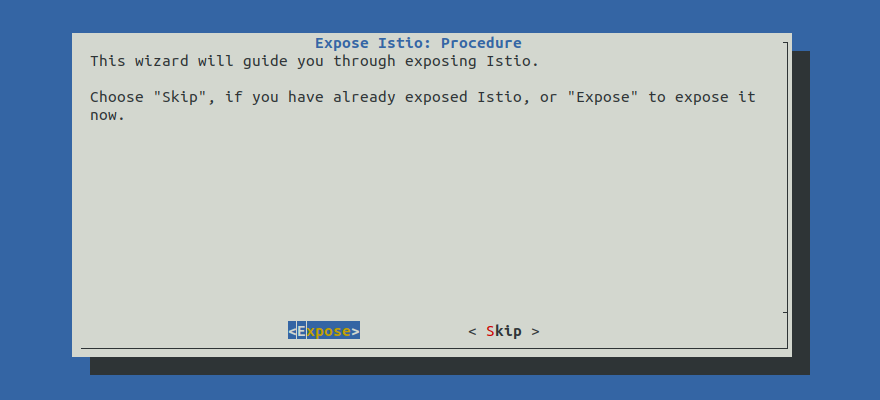
Expose Istio by following the on-screen instructions on the rok-deploy
user interface.
If rok-deploy is not already running, start it with:
Proceed to the Summary section.
Option 2: Expose Istio Manually¶
If you want to expose Istio manually, follow the instructions below.
Procedure¶
Go to your GitOps repository, inside your
rok-toolsmanagement environment:root@rok-tools:/# cd ~/ops/deploymentsRestore the required context from previous sections:
root@rok-tools:~/ops/deployments# source deploy/env.servingroot@rok-tools:~/ops/deployments# export SERVING_TYPE \ > SERVING_SUBDOMAIN SERVING_PREFIXSpecify the NGINX class to use. Choose one of the following options based on which NGINX you are using:
The Serving NGINX is used by default. Continue with next step.
Edit
rok/expose-serving/overlays/deploy/kustomization.yamland enable theingress-classpatch:patches: ... - path: patches/ingress-class.yamlEdit
rok/expose-serving/overlays/deploy/kustomization.yamland enable thexffpatch:patches: ... - path: patches/xff.yaml target: kind: EnvoyFilter name: xff-trust-hopsSet the number of trusted proxies in front of the Gateway:
root@rok-tools:~/ops/deployments# export SERVING_TRUSTED_FRONT_PROXIES=2Note
ALB acts as a L7 edge proxy so you have two proxies in front of Istio: ALB and NGINX.
Render the Istio envoy filter patch template with the variables you have specified:
root@rok-tools:~/ops/deployments# j2 \ > rok/expose-serving/overlays/deploy/patches/xff.yaml.j2 \ > -o rok/expose-serving/overlays/deploy/patches/xff.yamlEdit
rok/expose-serving/overlays/deploy/kustomization.yamland enable theingress-hostpatch by uncommenting the corresponding snippet. The final result will look like this:patches: - path: patches/ingress-host.yaml target: kind: Ingress name: knative-serving-ingress #- path: patches/ingress-tls.yaml #- path: patches/certificate.yaml - path: patches/xff.yaml target: kind: EnvoyFilter name: xff-trust-hopsNote
TLS termination takes place on the ALB with an ACM certificate, and thus you will create a plain HTTP ingress without any certificate.
Render the patch for Ingress rules:
root@rok-tools:~/ops/deployments# j2 \ > rok/expose-serving/overlays/deploy/patches/ingress-host.yaml.j2 \ > -o rok/expose-serving/overlays/deploy/patches/ingress-host.yamlCommit your changes:
root@rok-tools:~/ops/deployments# git commit -am "Expose Istio for Serving"Apply the kustomization:
root@rok-tools:~/ops/deployments# rok-deploy --apply rok/expose-serving/overlays/deployAir Gapped
In case of a private only EKS cluster, external-dns will not be able to update Route 53 entries automatically. So you have to manually create an alias record, i.e., an A record pointing to the internal ALB created by the AWS Load Balancer Controller.
Verify¶
Verify that you have successfully created the Ingress object for Istio. Ensure that the HOSTS field includes both your subdomain and your wildcard subdomain. Wait until the ADDRESS field shows the hostname of your load balancer:
root@rok-tools:~# kubectl get ingress -n knative-serving NAME CLASS HOSTS ADDRESS PORTS AGE knative-serving-ingress nginx-serving *.arrikto-cluster-serving.serving.example.com,arrikto-cluster-serving.serving.example.com e53a524a-ingressnginx-ingr-8872-592794601.us-east-1.elb.amazonaws.com 80 1m
What’s Next¶
Optionally, you can integrate Rok and Arrikto EKF with external platforms or projects.
