Grant Rok Access to Private Docker Registry¶
This guide will walk you through granting Rok access to Arrikto's GCP Container Registry.
The Arrikto provided dockerconfig.json file contains a token with pull
access to the arrikto-deploy GCP Container Registry. In order to pull
container images for Rok and its components, you need to copy this file in
certain locations under the kustomization tree of the GitOps repository.
Fast Forward
If you have already copied the dockerconfig.json file to the appropriate
locations, expand this box to fast-forward.
- Proceed to the Verify section.
Choose one of the following options to give Rok access to arrikto-deploy:
- Option 1: Grant Rok Access to Private Docker Registry Automatically (preferred).
- Option 2: Grant Rok Access to Private Docker Registry Manually.
Air Gapped
Follow Option 2 and proceed with the manual installation.
Overview
What You'll Need¶
- A configured management environment.
- Your clone of the Arrikto GitOps repository.
- Access to Arrikto's Private Registry.
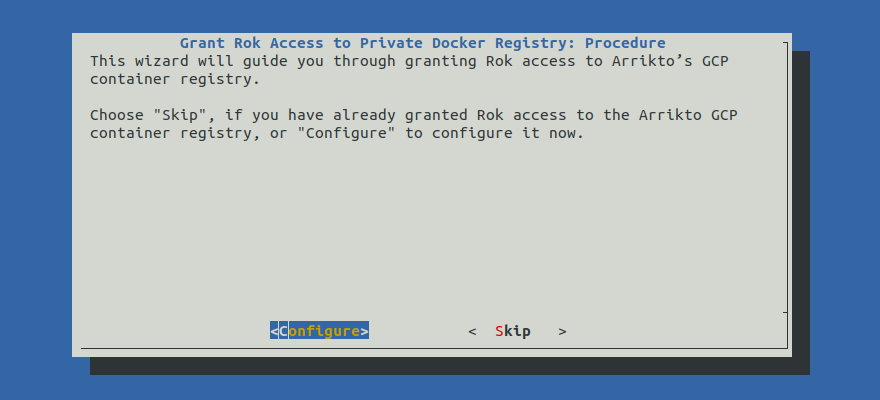
Option 1: Grant Rok Access to Private Docker Registry Automatically (preferred)¶
Grant Rok access to the arrikto-deploy container registry by following the
on-screen instructions on the rok-deploy user interface.
If rok-deploy is not already running, start it with:
root@rok-tools:~# rok-deploy --run-from pullsecrets
Proceed to the Summary section.
Option 2: Grant Rok Access to Private Docker Registry Manually¶
If you want to grant Rok access to the arikto-deploy container registry
manually, follow the instructions below.
Procedure¶
Go to your GitOps repository, inside your
rok-toolsmanagement environment:root@rok-tools:~# cd ~/ops/deployments
Copy
dockerconfig.jsonto the following locations:root@rok-tools:~/ops/deployments# cp deploy/dockerconfig.json \ > rok/rok-cluster/overlays/deploy/secrets/dockerconfig.json
root@rok-tools:~/ops/deployments# cp deploy/dockerconfig.json \ > rok/rok-operator/overlays/deploy/secrets/dockerconfig.json
root@rok-tools:~/ops/deployments# cp deploy/dockerconfig.json\ > rok/rok-disk-manager/overlays/deploy/secrets/dockerconfig.json
root@rok-tools:~/ops/deployments# cp deploy/dockerconfig.json \ > rok/rok-kmod/overlays/deploy/secrets/dockerconfig.json
Commit your changes:
root@rok-tools:~/ops/deployments# git commit -am \ > "Grant Rok Access to Private Docker Registry"
Mark your progress:
root@rok-tools:~/ops/deployments# export DATE=$(date -u "+%Y-%m-%dT%H.%M.%SZ")
root@rok-tools:~/ops/deployments# git tag -a deploy/${DATE?}/release-1.4/pullsecrets \ > -m "Grant Rok Access to Private Docker Registry"
Note
Kustomize will read these files, auto-generate Secrets, and pass them to
individual Rok components, so that they can pull from the arrikto-deploy
container registry on your behalf.
Air Gapped
Since you will end up using the mirrored images instead of the Arrikto-provided ones, follow the Set Up Cluster-Wide Authenticated Access to a Docker Registry guide to allow for pulling images from your internal registry. The ImagePullSecrets that you configured above will remain unused.
Verify¶
Go to your GitOps repository, inside your
rok-toolsmanagement environment:root@rok-tools:~# cd ~/ops/deployments
Build the manifests for each one of the four Rok components and make sure the
.dockerconfigjsonfields are not empty:root@rok-tools:~/ops/deployments# kustomize build rok/rok-cluster/overlays/deploy | \ > grep "\.dockerconfigjson" | cut -c -80 .dockerconfigjson: ezgGBltDd...
root@rok-tools:~/ops/deployments# kustomize build rok/rok-operator/overlays/deploy | \ > grep "\.dockerconfigjson" | cut -c -80 .dockerconfigjson: ezgGBltDd...
root@rok-tools:~/ops/deployments# kustomize build rok/rok-disk-manager/overlays/deploy | \ > grep "\.dockerconfigjson" | cut -c -80 .dockerconfigjson: ezgGBltDd...
root@rok-tools:~/ops/deployments# kustomize build rok/rok-kmod/overlays/deploy | \ > grep "\.dockerconfigjson" | cut -c -80 .dockerconfigjson: ezgGBltDd...
